Regarding encryption, a lot of people assume a file is secure as soon as it is encrypted – but sadly, this isn’t actually true. Still, encryption – being technology – does degrade with time, and the ways we presently protect information weren’t made to withstand the increasing processing strength we’ll have in the future. Because of this, quantum-resistant encryption is now part of what modern cybersecurity planning includes.
The core difficulty is the difference between how long we want to keep encrypted data, and how long the encryption we’re using will remain secure. We can’t be surprised by upcoming cyber attacks, and so, both companies and individuals are now thinking about encryption from a long-range viewpoint.
This post really investigates the security difficulties we have at the moment and shows how quantum-proof encryption, and things like QEncrypt, are solving these issues in a very sensible, practical manner.
The Hidden Frustration with Modern Encryption
The true trouble isn’t a shortage of resources; it’s putting too much trust in how long those resources will work. Quantum-resistant encryption operates on the idea that data security ought to cover the entire period the information exists, and employs a different sort of technology – things like QEncrypt – to allow groups and people to feel secure.
Data That Outlives Its Encryption
Files aren’t likely to be needed briefly. Things like significant paperwork, agreements, patents, health information, money matters and secret exchanges must be safeguarded for a long time – possibly for many years, even tens of years. Ordinary encryption doesn’t allow for this, and won’t deal with the problem of risk over a long period. Quantum-proof encryption was created to meet this demand, making sure that your files will not become impossible to read as the ability of computers improves in the future.
“Harvest Now, Decrypt Later” Is No Longer Theoretical
A worry, too, is the tactic often called “harvest now, decrypt later” doesn’t seem so unlikely as it once did. Because people are anticipating the time quantum computers arrive – ones that can decrypt things – hackers who want to break through encryption can gather and keep hold of data which is encrypted.
Threats, and quite famous ones at that, aim at data that is stored, back-ups, and archives; and it is these that companies and other groups think are securely shut away, though quantum-safe encryption solves this problem by making use of methods of encryption that will withstand both the ways of decryption which exist today and the ways which will be around in the future.
Traditional Encryption Wasn’t Built for Quantum Reality
RSA and ECC remain useful, though they weren’t at the start built to hold up against quantum computing attacks – and quantum computers, with their far better ability, will entirely overcome them. It isn’t a question of abandoning systems that have worked, however; instead we must accept that encryption which will be good for the future needs to be created anew, to deal with dangers at the quantum scale. Accepting this is a stage in the development of encryption, not something unusual, and is at the moment how we’re shaping new, present-day encryption norms.
Security Tools Are Too Complex to Use Consistently
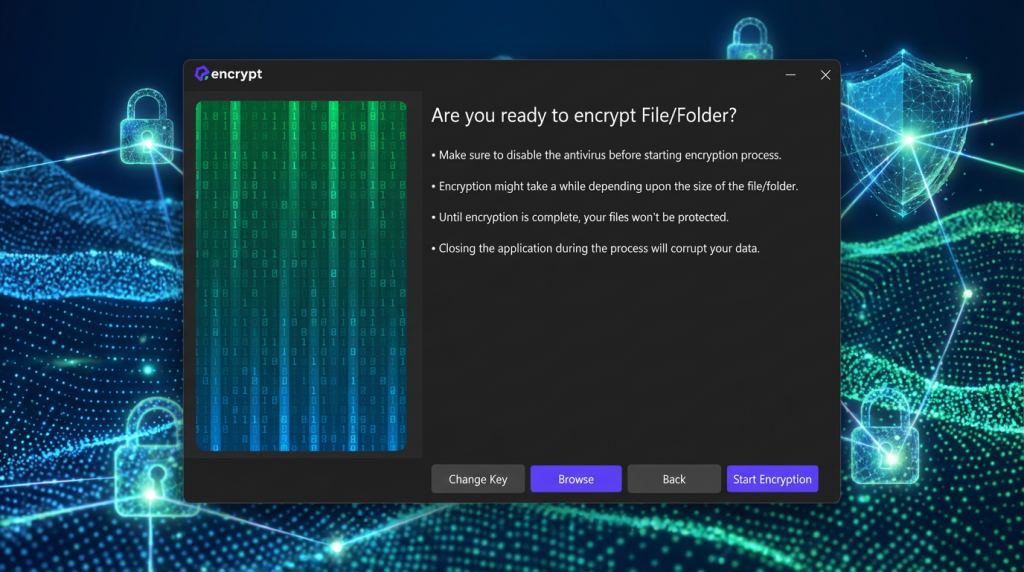
A really big issue in cybersecurity, as well, is how easy – or not easy – systems are to work with. Quite a lot of secure setups don’t function because they’re just too hard to get going, to oversee, or to regularly employ. If encryption programs are too complex, individuals will either avoid them or get them wrong. Quantum-proof encryption can work, however, if it’s direct, dependable, and uncomplicated enough to be used, and a great many of the concepts around it aren’t like that.
Future-Proofing Feels Disruptive and Expensive
Lots of organisations hesitate to adopt new encryption standards because they worry about the cost, disruption, and hassle, but replacing infrastructure, training their staff, and migrating their data feels like a monumental task that they can put off until the last minute, which they usually do.
Newer quantum safe encryption solutions are designed to slot into place, rather than tearing down what’s already there, and by getting started early, companies can greatly reduce the costs, knock out the need for future migrations, and spread the risk out over time.

How Quantum Safe Encryption Solves These Challenges
When it comes to cybersecurity, traditional encryption has three main challenges:
- Data will eventually become outdated
- It’s susceptible to future decryption methods
- Impractical to implement in real-world systems
But quantum safe encryption addresses all of these issues, and it provides you with:
- Long-term protection
- Resilient to potential decryption
- Easy to integrate into any system
This switch from a reactive to a proactive mindset allows you to safeguard both the data you already have and the risks that will come in the future.
How QEncrypt Makes Quantum Proof Encryption Practical
QEncrypt makes quantum-resistant encryption practical – offering a file security system people can use, and which doesn’t demand a lot of understanding of cryptography to actually encrypt and safeguard private papers. Rooted in ease, and with a view to working with what’s already there, and a pledge to be secure for years ahead, QEncrypt joins up involved encryption and routine data security.
Who Should Adopt Quantum Proof Encryption Now?
This isn’t just for corporations and governments anymore; quantum proof encryption is becoming necessary for the following:
- Any business that has confidential files
- Professionals who store client info
- Companies that have to keep records for a long time
- Individuals who are serious about their privacy and long-term security
Those who adopt it now will have a much smoother ride, whereas those who don’t will face costly and rushed migrations.
Why Acting Early Matters More Than Waiting
Those in the know – leading specialists – are warning that a poor plan is to put off altering your encryption until quantum computing is widely available; should criminals learn of the weaknesses, the expense of fixing the problems will greatly increase, and, on reflection, there isn’t a single solid reason not to use quantum-resistant encryption now.
More Value, Less Complexity: QEncrypt in the MindSuite Bundle
Assessing long-term security for your computer, buying QEncrypt as part of the MindSuite software bundle is not only cost-effective, but also provides you with clear financial savings.
- Coming in at $205.95 per year when bought separately, the cost of the included products escalates to $617.85 over the course of three years.
- Whereas, the MindSuite bundle that comes with QEncrypt can be had for $174.99 per year and $448.99 over three years, with the same quantum-safe encryption features thrown in for the price.
In addition to the price savings, the M
Conclusion:
When we talk about encryption, security isn’t only for protecting information as it stands – it’s about being certain that protection will continue. Quantum-safe encryption – which people also call post-quantum encryption – strengthens the usual security we have, and answers worries about how long data will stay safe, how easy it is to use in practice, and what problems may come up later. Well-known programs like QEncrypt allow us to start using security which resists quantum computers, and lets people and companies be comfortable with protecting important data, not only at this moment, but for a long time to come.