The digital world runs on trust, and that trust is built on encryption. Every financial transaction, private message, and sensitive business operation relies on cryptographic systems designed to keep data secure. However, a technological shift is approaching that threatens to break this foundation entirely: quantum computing. Unlike classical computers, quantum machines can process complex mathematical problems at unprecedented speeds, potentially rendering today’s encryption methods obsolete. Industry forecasts suggest that the global Post-Quantum Cryptography (PQC) market size is forecasted to grow remarkably from $0.42 billion in 2025 to $2.84 billion by 2030, at a CAGR of 46.2%, as organizations race to prepare.
This isn’t just a theoretical risk; it’s a strategic cybersecurity challenge unfolding now. To safeguard long-term data integrity and privacy, businesses and governments must begin transitioning toward quantum-safe cryptographic systems today, before existing protections fail.
What Is Post-Quantum Cryptography (PQC)?
PQC is a specialized field focused on developing encryption methods that remain secure against both classical and quantum computing attacks. Traditional cryptographic systems rely on mathematical problems that are computationally infeasible for classical computers to solve within a reasonable timeframe. However, quantum algorithms fundamentally change this assumption.
For instance, widely used encryption standards such as Rivest-Shamir-Adleman (RSA) and Elliptic Curve Cryptography (ECC) depend on the difficulty of factoring large numbers or solving discrete logarithms. Classical computers would take millions or even billions of years to solve these problems. But with quantum algorithms like Shor’s Algorithm, these same problems can potentially be solved in a matter of hours or even seconds.
This creates a critical vulnerability in modern cybersecurity infrastructure; even systems that are considered secure today could become easily breakable once sufficiently powerful quantum computers are developed. Importantly, not all cryptographic methods are equally vulnerable. Symmetric encryption algorithms like AES are more resistant to quantum attacks. While Grover’s Algorithm can reduce their effective security strength, this can be mitigated by doubling key sizes, for example, moving from AES-128 to AES-256.
Thus, PQC aims to replace vulnerable systems with algorithms based on mathematical problems that remain difficult even for quantum computers, ensuring long-term data protection.
Why Quantum-Resistant Encryption Matters Now
The urgency around quantum-safe encryption is driven by both technological progress and emerging attack strategies. One of the most concerning threats is known as “Harvest Now, Decrypt Later” (HNDL). In this scenario, attackers intercept and store encrypted data today with the intention of decrypting it in the future when quantum computing capabilities become available. This is particularly dangerous for data that must remain confidential for long periods, such as:
- Financial records
- Government communications
- Healthcare data
- Intellectual property
Even if quantum computers capable of breaking encryption are 10–15 years away, the data being transmitted today may still hold value decades into the future. This makes current encryption practices insufficient for long-term security.
Governments and regulatory bodies are already recognizing this risk. The U.S. National Institute of Standards and Technology (NIST) initiated its PQC standardization process in 2016, signaling early awareness of the quantum threat. Organizations that delay adopting quantum-safe strategies risk exposing themselves to future breaches, regulatory penalties, and loss of trust.
Core Quantum-Safe Cryptographic Approaches
To address quantum-era threats, researchers have developed several categories of quantum-resistant algorithms. Each approach is based on different mathematical principles and comes with unique advantages and trade-offs.
- Lattice-Based Cryptography
Lattice-based cryptography is widely considered the most promising solution for post-quantum security. It relies on the complexity of problems defined within high-dimensional lattice structures, such as the Learning With Errors (LWE) problem and the Short Integer Solution (SIS) problem.
These problems are computationally difficult to solve, even for quantum computers, making them strong solutions for future encryption systems. Lattice-based methods are also highly versatile, supporting encryption, digital signatures, and key exchange protocols. However, they often require larger key sizes and increased computational resources, which can impact system performance.
- Hash-Based Cryptography
This type of encryption uses cryptographic hash functions to create secure digital signatures. Unlike other methods, it does not rely on algebraic structures that could be vulnerable to quantum attacks. This approach is well-understood and has been studied extensively, making it a highly trusted option for specific use cases, particularly digital signatures.
The primary drawback is that hash-based signatures tend to be larger in size and may have limitations in terms of scalability and repeated usage.
- Multivariate Cryptography
Multivariate cryptography is based on solving systems of multivariate polynomial equations, which are extremely difficult to compute efficiently. This complexity provides strong resistance against both classical and quantum attacks. These systems are particularly useful for digital signature schemes. However, they often suffer from large public key sizes and practical implementation challenges, which can limit their adoption in real-world applications
The Role of NIST in Standardization
The National Institute of Standards and Technology (NIST) has played a central role in guiding the transition to quantum-safe cryptography. Its multi-year evaluation process brought together experts from academia, industry, and government to rigorously test and validate proposed algorithms. After several rounds of analysis, NIST announced its first set of standardized PQC algorithms in 2024. These include CRYSTALS-Kyber for key encapsulation and CRYSTALS-Dilithium for digital signatures
This standardization process is critical because it ensures that:
- Cryptographic algorithms are secure and reliable
- Systems can interoperate globally
- Organizations can adopt solutions with confidence
NIST’s approach emphasizes transparency, peer review, and real-world applicability, making its standards a cornerstone of global cybersecurity strategy.
PQC Adoption: Addressing Real-World Challenges
Despite the clear need for quantum-safe cryptography, implementation presents several challenges. Organizations must navigate technical, operational, and strategic complexities when transitioning from legacy systems.
One major issue is integration. Existing infrastructure was not designed with PQC in mind, making it difficult to retrofit new algorithms without significant changes. Additionally, quantum-safe algorithms often require more computational power, leading to performance trade-offs.
Another challenge is the need for crypto-agility, the ability to quickly switch between cryptographic algorithms as new standards emerge or threats evolve. Without this flexibility, systems risk becoming outdated or vulnerable. There is also a shortage of skilled professionals with expertise in post-quantum cryptography, which can slow adoption and increase implementation risks. To overcome these challenges, organizations must take a proactive and strategic approach, starting with risk assessments and pilot implementations.
Lattice-Based Cryptography: The Front Runner
Among all PQC approaches, lattice-based cryptography has emerged as the leading candidate for widespread adoption. Its strong theoretical foundation, combined with practical performance characteristics, makes it suitable for real-world deployment. The Learning With Errors (LWE) problem, a core component of lattice-based systems, introduces controlled randomness into equations, making them extremely difficult to reverse-engineer. This property provides robust protection against both classical and quantum attacks. These algorithms have already been selected by NIST and are being integrated into modern security protocols. Their flexibility allows them to be used across a wide range of applications, from secure communications to cloud infrastructure.
As organizations begin transitioning to quantum-safe systems, lattice-based cryptography is expected to play a central role in shaping the future of encryption.
Preparing for a Quantum-Safe Future
Transitioning to quantum-safe cryptography requires careful planning and long-term commitment. Organizations should begin by identifying critical data assets and assessing their exposure to quantum risks.
Key steps include:
- Conducting cryptographic audits
- Prioritizing long-term sensitive data
- Implementing hybrid encryption models
- Aligning with NIST standards
- Building crypto-agile systems
Early adoption not only reduces future risk but also provides a competitive advantage in industries where data security is paramount.
Are You Prepared for the Future?
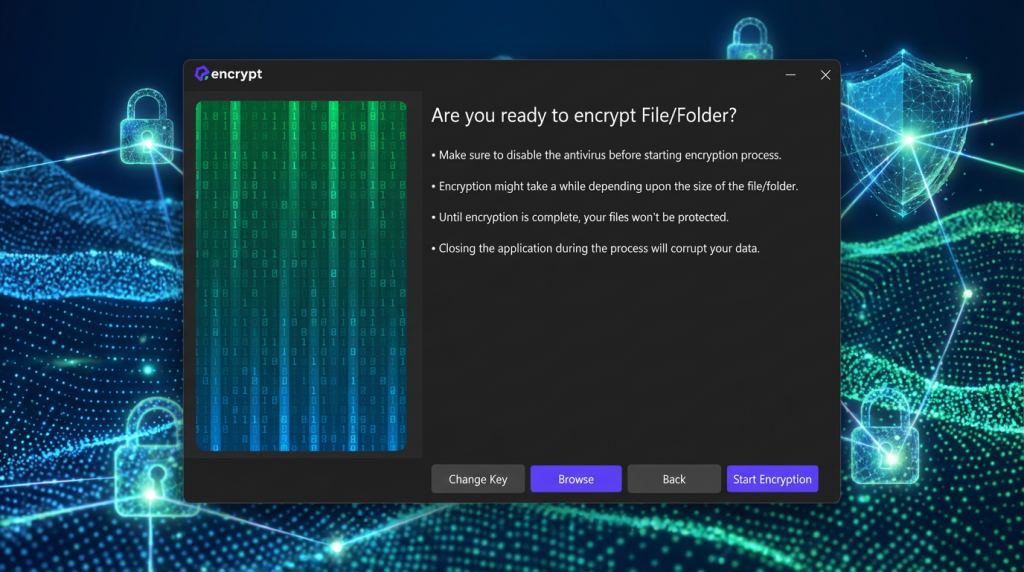
Quantum computing represents both an extraordinary technological breakthrough and a profound cybersecurity challenge. As the ability to break traditional encryption becomes increasingly realistic, the need for quantum-safe cryptography grows more urgent. Post-quantum solutions, built on advanced mathematical foundations and validated through global standardization efforts, offer a clear path forward. However, the transition is complex and requires immediate action, strategic planning, and continuous adaptation. This is where tools like QEncrypt have emerged, aiming to help organizations dealing with sensitive data prepare today to fight the quantum-era security risks.
Organizations that invest in quantum-resistant security today will be better positioned to protect sensitive data, maintain regulatory compliance, and preserve customer trust in the years ahead. In a world where data is one of the most valuable assets, preparing for the quantum era is not just a technical necessity; it is a business imperative that will define long-term resilience and security.
Want to secure your business data from quantum-era cyberattacks?
