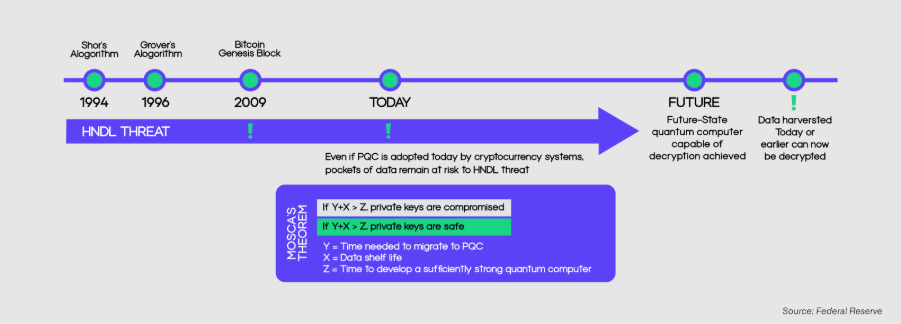
Password-based encryption has long been the foundation of digital trust. Every organisation operates on the belief that encryption keeps data safe, not just today, but indefinitely. But with the emergence of a new threat model, Harvest Now, Decrypt Later (HNDL), this belief is about to break. Instead of immediately manipulating encryption, cyber attackers are shifting strategies. They are gathering encrypted data today, storing it at scale, and waiting for the right moment when quantum computing advances, making decryption possible.
This changes everything. The breach doesn’t happen when the data is decrypted, it happens the moment it is compromised. With the quantum computing market projected to reach $5.09 billion in 2026, growing at over 40% annually, the timeline for these risks is accelerating. What once felt like a distant possibility is quickly becoming an inevitable reality, forcing organizations to rethink how long their data can truly remain secure.
What Is “Harvest Now, Decrypt Later”?
Harvest Now, Decrypt Later is a long-term cyberattack strategy built on patience and inevitability. Instead of decrypting confidential records in real-time, a process that requires exceptional computing power, cyber attackers focus on collecting encrypted data now and decrypting it later.
The process is straightforward but powerful:
- Harvest Now: Collect encrypted data through breaches, phishing attacks, or account takeover fraud.
- Store Indefinitely: Archive massive volumes of encrypted data at low cost.
- Decrypt Later: Use quantum computing to decrypt the data.
What makes this cyberattack strategy particularly dangerous is that it does not require immediate success; impostors do not need to break encryption in real-time. They only need to ensure they have loads of data until the necessary decryption tools become available.
This fundamentally reframes encryption. It is no longer a permanent barrier that keeps data secure, but a time-bound safeguard. If the value of the data persists longer than the strength of the encryption protecting it, then the data can be exposed easily, just on a delayed timeline.
Why This Threat Exists Today, not in the Future
One of the biggest misconceptions about Harvest Now, Decrypt Later is the belief that it’s a future problem closely linked with the arrival of quantum computers. However, the truth is, this threat is already active as data harvesting is happening now.
Some of the few categories of sensitive data are inherently long-lived:
- Medical and genetic records may remain relevant for a lifetime.
- Financial and legal records often require decades of confidentiality.
- Government and defence communications may need to remain secret indefinitely.
- Intellectual property can retain value for decades.
Thus, it’s evident that current pre-quantum encryption algorithms securing organizational data, such as Rivest-Shamir-Adleman (RSA) and Elliptic Curve Cryptography (ECC), are not powerful enough to resist quantum attacks. Once quantum computers reach a sufficiently advanced stage, these widely used systems could become obsolete. Therefore, with growing awareness of Harvest Now, Decrypt Later, it has been found that almost 60% of businesses now view HNDL as a major threat, particularly for information having value beyond 2030.
How the HNDL Attack Actually Works
Despite its long-term implications, the mechanics of HNDL are relatively simple and rely heavily on existing cyberattack methods. The following is an example of how this attack works.
Data Harvesting
The first stage involves gathering encrypted data from as many sources as possible. This can include:
- Intercepting encrypted internet traffic
- Breaching cloud storage or enterprise databases
- Accessing backups or archives
- Exploiting vulnerabilities in third-party systems
The thing to be noted here is that attackers are not trying to decrypt anything at this stage. They are simply stockpiling valuable data.
Silent Data Storage
Once data is collected, it is stored for future use. Advances in storage technology have made it easy to maintain large datasets for long periods at a very cheap cost, allowing attackers or well-funded groups to build extensive archives of encrypted information.
This stage is completely invisible. Organizations have no practical way of knowing that their encrypted data has been copied and stored elsewhere.
Future Decryption
The final stage occurs when technology catches up. With the development of Cryptographically Relevant Quantum Computers (CRQCs), cyber attackers can apply algorithms like Shor’s to break encryption schemes that are currently considered secure. At that point, previously inaccessible data becomes fully readable.
Which Industries are Most at Risk?
HNDL is not about opportunistic attacks, it is about strategic data collection. As a result, attackers prioritize data that will retain value over long periods.
The most at-risk sectors include:
- Financial Services: Transaction histories, banking data, contracts
- Healthcare: Patient records, genomic data, research
- Government and Defence: Classified communications and intelligence
- Technology and R&D: Patents, proprietary algorithms, product designs
The stakes are enormous. According to recent economic analysis, a single quantum-enabled breach affecting a major financial institution in the United States could result in $2.0 to $3.3 trillion in damages. This highlights why HNDL is not just a cybersecurity issue, it is a systemic economic risk which can only be secured using quantum proof encryption methods.
Q-Day: The Role of Quantum Computing
Quantum computers are the key technological driver behind HNDL. Unlike traditional computers, quantum systems can solve big mathematical problems at an exponential speed, particularly those algorithms underlying classical encryption. Q-Day generally refers to the point at which quantum computers will become capable of manipulating widely used cryptographic algorithms at scale. While the exact timelines are uncertain, tech industry leaders and governments are already preparing for a transition window between 2030 and 2035.
Key milestones include:
- 2030: Deprecation of legacy encryption algorithms like RSA and ECC
- 2035: Full transition to quantum-resistant cryptography for federal systems
However, this timeline is not speculative planning; it is an active, global effort to prepare for a known disruption. This is why it’s estimated that the Post-Quantum Cryptography (PQC) market is projected to grow from $1.35 billion (2025) to $22.68 billion by 2033.
The Real Risk: Time-Delayed Breaches
HNDL has emerged as a new type of cybersecurity risk; data breaches remain invisible until it’s too late.
Traditional breaches are immediate and reactive:
- Systems are compromised
- Alerts are triggered
- Responses are initiated
While HNDL operates on a delayed timeline:
- Data is stolen silently
- No alerts are generated
- Impact will be visible after years or decades
Thus, HNDL issue creates significant challenges:
- Organizations cannot respond to a breach they don’t know occurred.
- Cybersecurity systems are not designed for delayed exposure.
- Sensitive information may be circulating publicly while assuming it’s stored safely.
The thing to be considered here is that this systemically engineered cyberattack strategy is particularly dangerous from both regulatory and technical perspective.
Rethinking Security: From Strength to Longevity
The technological shifts in cyberattack techniques and the emergence of Harvest Now, Decrypt Later are forcing organizations to rethink their encryption protocols. For decades, the focus has been on strength, choosing fool-proof algorithms that are difficult to break, but HNDL introduces a new requirement: Longevity.
Organizations must now evaluate:
- How long do they need to store confidential data
- Whether current encryption and cybersecurity measures can help them secure confidential data
- How quickly can they adapt to new cybersecurity protocols
How to Defend Against HNDL
Addressing and combating HNDL requires a proactive and strategic approach. Waiting for quantum computers to arrive is not an option. The following are the critical steps that are not just defensive but are essential for developing future-ready cybersecurity architectures:
1. Identify Long-Term Sensitive Data: Understand which data assets require long-term confidentiality and prioritize them for enhanced protection.
2. Adopt Post-Quantum Cryptography (PQC): Begin transitioning toward quantum-resistant algorithms that can withstand future attacks.
3. Build Crypto-Agile Infrastructure: Ensure systems can quickly adapt to new cryptographic standards without major disruption.
4. Reduce Data Retention: Limit how long sensitive data is stored. Reducing exposure reduces risk.
5. Secure Data Across Its Lifecycle: Protect data in transit, at rest, and during processing to minimize interception opportunities.
The Road Ahead and Where QEncrypt Fits In
Harvest Now, Decrypt Later is more than just a new cyber-attack strategy, it represents a fundamental shift in how organizations must understand and manage data security risk. One thing is clear: HNDL highlights a critical truth that cybersecurity decisions made today will determine whether confidential information remains secure years from now. This makes the adoption of post-quantum encryption not just a future upgrade, but an immediate necessity. As the world approaches the 2030–2035 quantum transition window, organizations face a rapidly narrowing opportunity to act.
This is where platforms like QEncrypt become essential. The next generation of cybersecurity is not just about reacting to threats but anticipating them. QEncrypt is built around this principle, enabling organizations to move toward quantum-resilient encryption, crypto-agility, and long-term data protection strategies that align with the realities of HNDL.
Rather than treating encryption as a static solution, this tool helps organizations rethink it as an evolving system. Because in a world where attackers are already harvesting encrypted data, the real measure of security is not whether your data is protected today. But whether it will still be protected when the future arrives.
