For decades, AES, ECC, and RSA have formed the backbone of global cybersecurity, safeguarding financial systems, government communications, and digital identities. The existing encryption strategies were developed on complex mathematical problems, with an assumption that a traditional computer would take thousands of years to break. But that assumption is increasingly becoming outdated.
As quantum computing advances, today’s trusted encryption systems face a fundamental risk. The question is no longer whether they will fail, but when. And for sectors holding long-lived sensitive data, that timeline may already be too late.
According to industry projections, the global post-quantum cryptography market is expected to reach $1.58 billion by 2026, growing at a staggering 49.4% CAGR through 2034. This rapid growth reflects a critical shift that organizations are no longer treating quantum risk as theoretical, but they are actively investing in quantum-resistant cryptography solutions.
Thus, the transition towards quantum-safe encryption is no longer optional; it’s inevitable.
The Illusion of Security in a Pre-Quantum Encryption World
Today’s encryption methods have earned their reputation through years of resilience. RSA, AES, and ECC have withstood extensive academic scrutiny, real-world cyberattacks, and evolving computational capabilities.
However, this long-standing reliability has created a dangerous assumption that what has worked in the past will also work in the future. This confidence is rooted in a specific limitation of classical computing power.
Traditional computers rely on sequential processing, which makes certain mathematical problems practically unsolvable within a reasonable timeframe. Encryption standards were developed around these limitations. The problem here is that these limitations no longer define the future of computing.
Cybersecurity protocols today are evaluated based on current cyber-attack capabilities, not quantum-backed breaches. This creates a gap between perceived security and actual future risk. Organisations continue to encrypt sensitive information under the assumption that it will remain secure for years to come, without considering how advancements in quantum computing could invalidate that protection.
Thus, companies operating in this illusory state are putting their long-lived data vulnerable to future cyber-attack strategies.
Why RSA, AES, and ECC Work Today, But Fail Against Quantum Encryption
To understand the urgency behind quantum encryption, it’s important to examine why current encryption systems are secure today.
- Rivest Shamir Adleman (RSA): Relies on the difficulty of factoring large composite numbers into their prime components. While simple in concept, this becomes computationally infeasible as key sizes grow, making brute-force attacks impractical for classical systems.
- Elliptic Curve Cryptography (ECC): Achieves similar security with smaller key sizes by relying on the complexity of solving discrete logarithm problems over elliptic curves. This efficiency has made ECC widely adopted in mobile devices, IoT systems, and modern secure communications.
- Advanced Encryption Standard (AES): Operates differently. As a symmetric encryption algorithm, it uses the same key for encryption and decryption. Its strength lies in the sheer number of possible key combinations, making brute-force attacks computationally unrealistic under classical constraints.
Together, these algorithms form the foundation of the current encryption ecosystem. However, they were never formed to secure systems from quantum attacks. As a result, RSA, ECC, and AES are fundamentally incompatible with the future of quantum-resistant encryption and post-quantum encryption standards.
Quantum Encryption and the Computing Revolution Breaking Cryptography
Quantum computing represents a paradigm shift, not an incremental improvement. Instead of processing bits as 0s and 1s, quantum computers use qubits, which can exist in multiple states simultaneously. Combined with entanglement, this makes quantum computers capable of evaluating vast numbers of possibilities in parallel. This fundamentally rewrites computational feasibility and highlights why quantum encryption is becoming essential.
Following are the two quantum algorithms that are particularly considered disruptive:
Shor’s Algorithm
Capable of factoring large integers and solving discrete logarithms exponentially faster than classical algorithms. This directly undermines RSA and ECC, making them obsolete in a quantum-enabled world.
Grover’s Algorithm
Provides a quadratic speedup for brute-force searches, reducing the effective strength of symmetric encryption like AES.
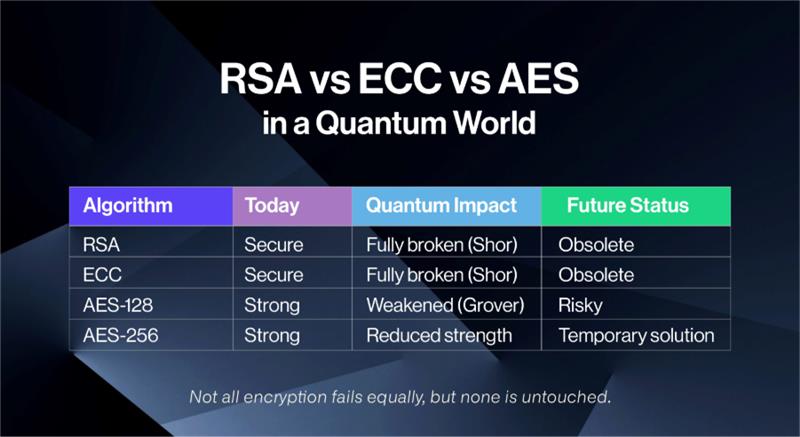
The aftermath of the emergence of quantum computers is clear:
- RSA and ECC will be fully broken
- AES will be weakened without adaptation
- Existing systems will fail without quantum safe cryptography
This is why organizations are rapidly exploring post quantum cryptography and quantum resistant encryption strategies to stay ahead of disruption.
Quantum Encryption vs “Harvest Now, Decrypt Later” Threats
One of the key drivers behind quantum encryption adoption is the “Harvest Now, Decrypt Later” (HNDL) strategy. In this model, attackers gather and store encrypted data today, even though they can’t decrypt it immediately. Once quantum computers become a reality, they can decrypt it retroactively.
This creates a delayed but devastating breach scenario:
- Sensitive communications exposed years later
- Intellectual property instantly compromised
- Long-term data confidentiality completely broken
Unlike conventional cyberattacks, HNDL works silently. Organizations may never come to know about the breach until it’s too late. This is the reason why quantum-safe encryption is becoming a critical part of cybersecurity strategy.
Why Quantum Encryption Matters for Every Industry
The shift towards quantum-safe encryption is not limited to financial institutions or government agencies, but it affects every sector that relies on encryption, which comprises of all of them.
Industries at most risk include:
- Financial services securing transactions
- Healthcare protecting patient data
- Technology companies safeguarding intellectual property
- Cloud providers managing global data infrastructure
Even small to medium-sized businesses are vulnerable through supply chain exposure. As global regulations evolve, quantum-resistant cryptography and quantum-safe encryption will most likely become a compliance obligation, aiming to secure businesses’ confidential data. Companies failing to comply will not only suffer data loss but also hefty regulatory penalties.
AES and the Limits of Partial Quantum Resistance
AES is often seen as a safe alternative in a quantum world, but this perception is misleading as Grover’s algorithm reduces its effective security:
- AES-128 → ~64-bit security
- AES-256 → ~128-bit security
While AES-256 remains usable, it is not a complete solution. However, it must be integrated into a broader post-quantum encryption strategy. Without secure key exchange and authentication mechanisms, this algorithm alone can’t deliver true quantum-resistant encryption. That’s the reason why organizations must adopt a holistic approach to quantum cryptography rather than relying on isolated security fixes.
The Migration Challenge to Quantum Safe Encryption
Migrating from current security protocols to quantum-safe cryptography is one of the most complex and challenging parts in modern cybersecurity.
Key issues include:
- Deep integration of RSA and ECC across systems
- Hardware limitations in IoT and embedded devices
- Performance trade-offs in new algorithms
- Lack of internal expertise
- High operational risk during transition
Unlike past enhancements, this transition impacts entire cybersecurity infrastructures. Shifting to post-quantum cryptography requires careful planning, phased implementation, and long-term investment. However, companies that delay will pay higher costs and experience increased risk under rushed migration pressure.
The Rise of Post Quantum Cryptography (PQC) and Quantum Encryption Standards
PQC is the foundation of future-ready cybersecurity strategy. It focuses on algorithms that remain secure against both traditional and quantum attacks.
These include:
- Lattice-based cryptography
- Hash-based signatures
- Code-based systems
- Multivariate cryptography
These encryption approaches form the backbone of quantum-resistant encryption and quantum-safe cryptography. However, implementing PQC is not just a technical transformation; it’s a strategic change.
Quantum Encryption with QEncrypt: Leading the Future of Security
As organizations move toward quantum encryption, QEncrypt is emerging as a market leader in delivering next-generation quantum safe encryption solutions.
Unlike traditional approaches, QEncrypt is built specifically for the quantum era. It enables organizations to adopt post quantum encryption without disrupting existing infrastructure.
Key capabilities include:
- Crypto agility for seamless algorithm transitions
- Hybrid encryption models combining classical and PQC approaches
- End-to-end quantum resistant encryption across data states
- Scalable deployment across cloud and enterprise environments
The tool is designed to counter real-world threats like “harvest now, decrypt later,” ensuring that data remains secure not just today, but in a quantum future. By focusing on proactive defence rather than reactive upgrades, QEncrypt defines what true quantum-proof encryption should look like.
Building a Future-Proof Quantum Encryption Strategy
To get competitive advantage in the post-quantum era, organizations must adopt the following approaches:
- Crypto Agility: Enable systems to switch between algorithms without major disruption.
- Data Prioritization: Focus on protecting long-lived sensitive data.
- Hybrid Encryption: Combine classical and post quantum encryption during transition.
- Continuous Risk Assessment: Monitor evolving threats and adapt accordingly.
- Vendor Alignment: Partner with providers leading innovation in quantum-safe encryption.
Final Thoughts
The foundations of RSA, AES, and ECC are no longer sufficient for the future. Quantum computing is redefining what it means to be “actually” secure, exposing the shortcomings of classical encryption systems. This is not a distant threat; it’s already shaping how attackers operate and how organizations must respond. The rise of HNDL makes it clear that today’s encrypted data will not be safe tomorrow. The shift to quantum encryption, quantum-resistant cryptography, and post-quantum cryptography is already underway.
Organizations that embrace the change early will lead the next era of cybersecurity. And those who will wait will be forced to catch up under pressure.
Ready to be part of this transition?
