Quantum computing is improving much faster than anyone predicted. In our current world where almost, everything is done on computers, encryption is what makes secure operation possible; it safeguards all kinds of information, digital banking, confidential conversations, and items that are not connected to the internet, are a few examples.
As technology advances, security threats do as well. Encryption techniques that used to be completely safe are now vulnerable to quantum computing. Quantum computers are still under development, but their abilities are now a reality, not simply a possibility.
This article will explain what quantum-safe encryption is, its mechanisms, and, above all, its increasing importance for protecting data for the future.
What Is Quantum-Safe Encryption?
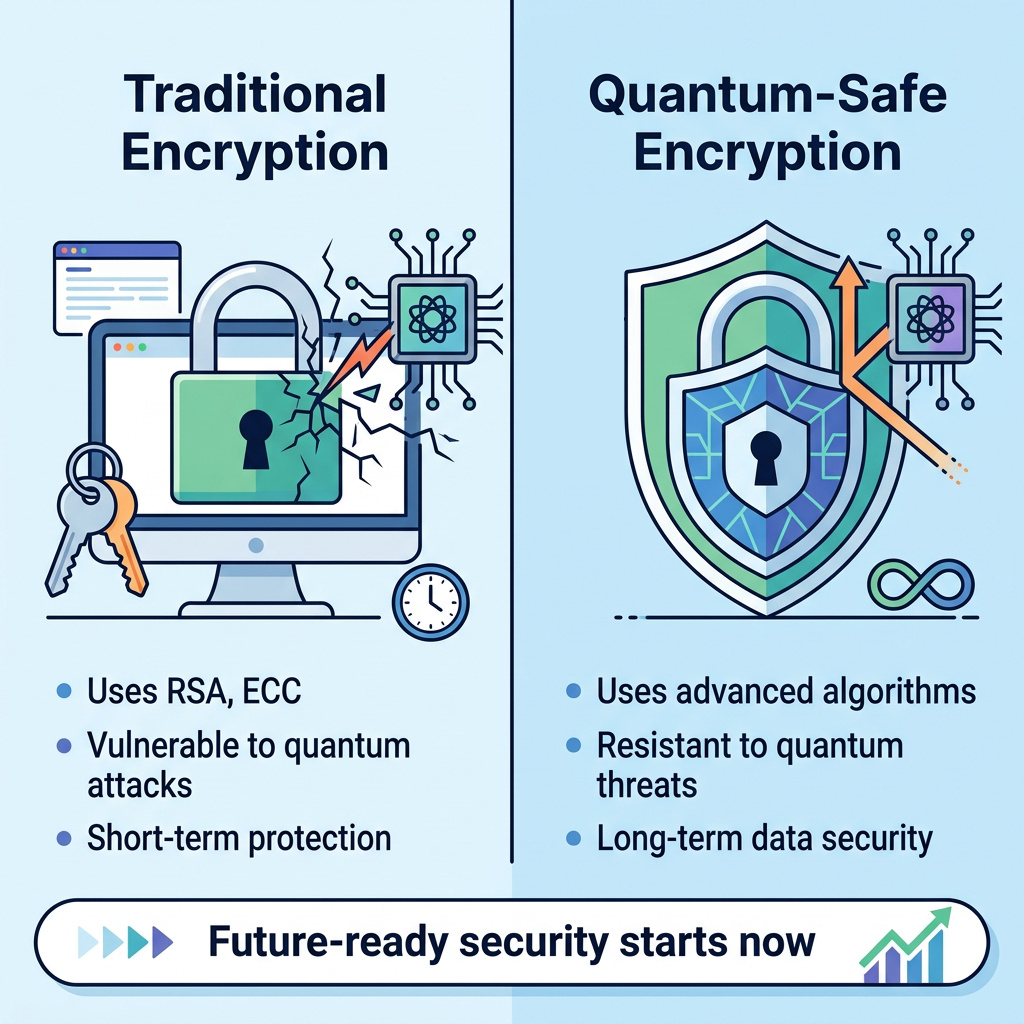
Quantum safe encryption, or quantum-resistant encryption, describes encryption techniques developed to stay secure even when facing attacks from quantum computers. These algorithms, in contrast to current encryption, are being built to defend against both standard and quantum computing methods of breaking them.
Most of the encryption we use today depends on mathematical difficulties which are extremely hard for traditional computers to break. Quantum computers, operating on completely different principles, will be able to solve these problems far more quickly, and utilize approaches including lattice-based cryptography, hash-based signatures, and code-based encryption.
For this reason, the encryption we currently employ is likely to be rendered ineffective when quantum computers are available on a large, usable scale. Simply put, quantum-safe encryption is about protecting data security for the long term, making certain that confidential details will be safe to use now, and will remain so for many years ahead.
Why Today’s Classical Encryption Methods Are at Risk
To know which encryption methods will work securely when quantum computers exist, we must first understand how current traditional encryption protect data and what will be its significance in post-quantum era.
Today’s most widely used encryption systems include:
- Rivest–Shamir–Adleman (RSA)
- Elliptic Curve Cryptography (ECC)
- Advanced Encryption Standard (AES)
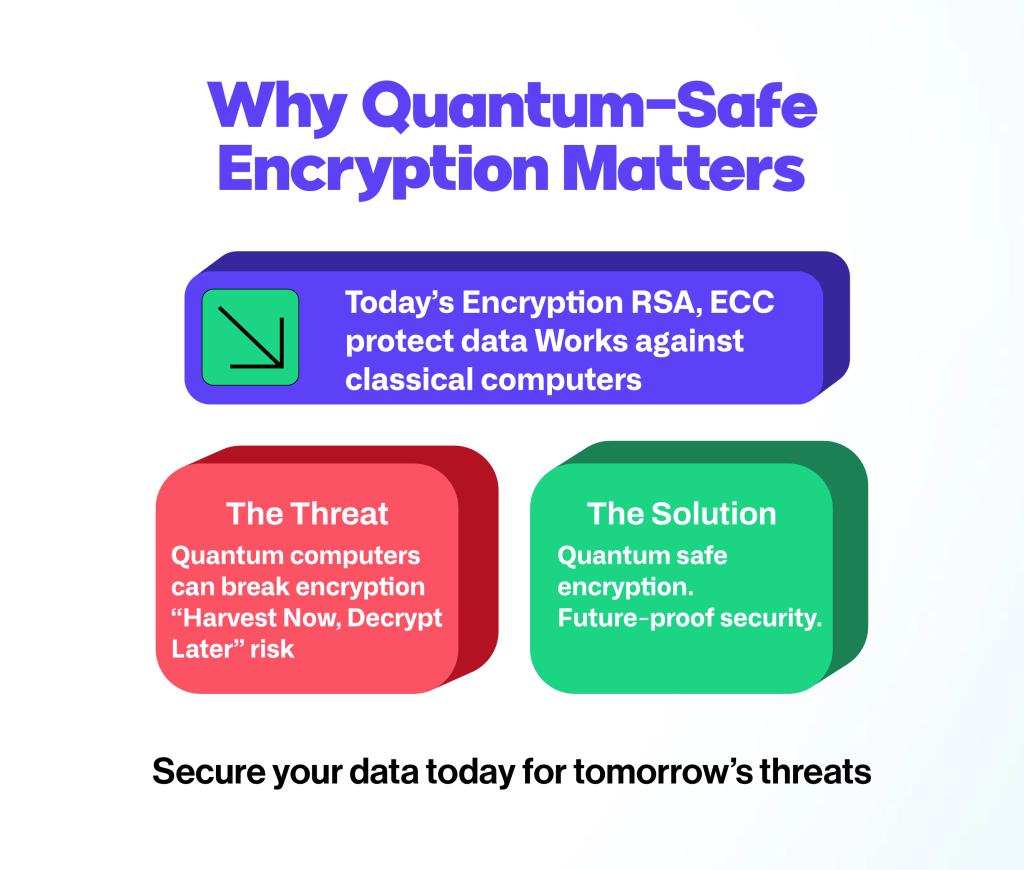
Currently, RSA and Elliptic Curve Cryptography (ECC) are heavily based on the complexity for ordinary computers of factoring enormous numbers and resolving discrete logarithms. Because of the difficulty for standard computers, these encryption methods have been considered reliable for a long time.
Quantum computers, though, utilise Shor’s Algorithm to find the solutions to these problems much more rapidly. Consequently, when quantum computing fully develops, RSA and ECC could be compromised in hours, or even minutes.
Advanced Encryption Standard (AES) is stronger against this, but it isn’t entirely protected. Quantum methods, such as Grover’s Algorithm, can lower AES’s actual security level and therefore create a weakness with the passage of time. This means that current encryption methods will soon be obsolete and will not work in the post-quantum era.
Quantum-Resistant Encryption: How it Works
Quantum-safe encryption uses different kinds of mathematical equations that we believe will hold up against attacks from quantum computers. Being based on the tricky calculations of discrete logarithms or factoring, these encryption techniques are designed around problems that are hard to break, even for quantum computers.
Some of the most promising quantum-safe encryption approaches include:
1. Lattice-Based Cryptography
This method depends on lattices, a complicated geometrical form, and even quantum computers find it exceptionally difficult to solve problems related to lattices, making this technique a prime option to secure data in the post-quantum era.
2. Hash-Based Cryptography
Cryptographic hash functions generate safe digital signatures, thoroughly understand hash-based cryptography, and provide significant protection against quantum computer-based assaults.
3. Code-Based Cryptography
Code-based cryptography, utilizing error-correcting codes, has a long history of examination and continues to be a robust choice for encryption which will withstand the power of quantum computers.
4. Multivariate Cryptography
Solving these problems requires dealing with complicated systems of equations with many variables, and even the power of quantum computers struggles with them. All these techniques are within quantum computing cryptography, a larger discipline dedicated to creating secure communications and data protection for the time when quantum computers are common.
Harvest Now, Decrypt Later: The Real Threat
People are getting increasingly worried about switching to encryption that quantum computers can’t break because of a strategy criminals are using called “Harvest now, decrypt later.” Essentially, they are grabbing any encrypted information they can get their hands on now and saving it. They can’t understand it now, but the idea is to hang on to it until quantum computers get good enough to break the current encryption, and then suddenly all that old data is open to them.
This is an alarming problem for information that needs to stay confidential for a long time, for example, bank details, government secrets, exclusive research, or medical history. What looks safe with today’s security could become completely useless, almost instantly, as quantum computers get to a certain power.
So, getting quantum-proof encryption isn’t just about being ready for the future; it’s about defending data that may already have been stolen and is being held for later. Companies and institutions that don’t make this change could well discover that their most important secrets have, as far as they are concerned, been open for years by the time they discover the problem.
Why Quantum-Safe Encryption Matters Now
Quantum computers that work are still in progress, yet they are likely to arrive sooner than previously thought. Many in the field estimate substantial progress will be achieved in the next ten years.
Therefore, companies and institutions need to begin preparing immediately and with urgency. Transitioning to quantum-safe encryption is a complex process that involves:
- Identifying vulnerable systems
- Updating cryptographic infrastructure
- Ensuring compatibility with new standards
Furthermore, authorities and governing bodies are already encouraging this shift. Standards bodies are busily creating plans for cryptography after the quantum era to help with this change.
Delaying action could result in:
- Data breaches in the future
- Compliance issues
- Loss of customer trust
However, being among the first to implement these changes will give a company an advantage over its rivals, and will show it is dedicated to protecting information for the future.
Best Practices for Getting Started
Transitioning to quantum-safe encryption doesn’t have to happen overnight. However, organizations should begin taking steps now. They must:
- Conduct a Cryptographic Inventory: Identify where and how encryption is used across your systems.
- Assess Risk Exposure: Determine which data is most vulnerable to future decryption threats.
- Adopt Hybrid Approaches: Combine traditional and quantum-safe encryption during the transition period.
- Stay Updated on Standards: Follow developments in post-quantum cryptography to ensure compliance.
- Work with Experts:Partner with cybersecurity providers who specialize in quantum-safe solutions
The Future of Encryption in a Quantum World
Adopting encryption methods that quantum computers can’t crack will be a truly historic shift in keeping organisations’ data safe. Just as the internet revolutionised communication, quantum computing is going to dramatically reshape how we secure information.
We’ll probably see things happen quickly – official, accepted quantum-safe methods, more and more businesses using them, these protections becoming part of the devices and software we use daily, and ongoing invention of new ways to scramble and safeguard things. The point isn’t just to fix things once quantum computers start ruining our current security, but to build a system that’s solid, ready for anything and will last into the future.
Prepare for the Post-Quantum Era with QEncrypt
Quantum computing is moving from being a dream to something that’s actually happening, and it’s going to completely change the world of protecting information. The ways we scramble things to keep them secret today, which have worked up to now, just won’t be powerful enough to withstand what a quantum computer can figure out.
Therefore, switching to encryption that can stand up to quantum computers is urgently needed and absolutely vital. Using encryption built to be quantum-resistant, and generally using cryptographic techniques that are ‘quantum safe’ will allow businesses and others to protect their data from what’s coming, maintain people’s confidence in them, and satisfy all the rules they have to follow.
It is critical to begin preparing now. To wait for quantum computers to be widely available will be too late to protect confidential information that is already vulnerable. Instead, companies should start to change to the new system now, carefully planning for a more secure future.
QEncrypt is a key example of how this is being done, assisting businesses in setting up encryption plans that are designed for the time of quantum computing, and ensuring data protection, however the future of technology unfolds.
