Data encryption has always stayed one step ahead of cybercriminals, until now. For decades, the cybersecurity systems safeguarding our communications, financial information, and digital identity have relied on mathematical problems that were impossible to crack using traditional computers. But with advances in quantum computing, that equation is changing entirely. A sufficiently powerful quantum machine can break widely used 2048-bit RSA encryption in just 8 hours, a task that would take classical computers billions of years.
Thus, governments and organizations are no longer treating this situation as a “maybe.” The market for quantum-resistant systems is accelerating rapidly, with post-quantum cryptography estimated to touch $1.58 billion by 2026, growing at 49.4% CAGR through 2034. This is why quantum encryption is no longer a theoretical concept; it’s becoming a critical priority.
The Fragile Foundation of Today’s Cryptography
Classic cryptography is sustained on a simple but powerful assumption that some mathematical problems are too difficult to solve within any reasonable timeframe.
This assumption underpins widely used systems such as:
- Rivest–Shamir–Adleman (RSA)
- Elliptic Curve Cryptography (ECC)
- Diffie-Hellman Key Exchange
These systems rely on “one-way functions” operations that are easy to perform but extremely difficult to reverse without the correct key. For instance, multiplying two large, odd numbers is simple, but factoring the result back into those odds is computationally intensive. In traditional computing terms, breaking RSA-2048 would require an astronomical amount of energy and time, far beyond practical limits. That’s the main reason why this algorithm has remained a global standard for securing everything from banking systems to HTTPS connections.
However, this trust is rooted in computational limitations, not absolute security. While the rise of quantum-resistant cryptography highlights a critical truth that once those computational limits are removed, the whole security system collapses. Due to this reason, organizations are increasingly shifting towards quantum safe cryptography, not because the classical systems are broken today, but because they will be after 2030.
What Makes Quantum Computing a Real Threat
Quantum computing represents a fundamental transition from classical computing, not just in terms of speed but in logic. Modern-day computers process information in binary bits (0s and 1s), while quantum computers use qubits, which can exist in multiple states simultaneously due to superposition. This gives quantum computers a competitive edge to evaluate many possible solutions at once. Moreover, entanglement creates correlations between qubits that maximize computational efficiency in ways traditional systems cannot replicate.
This results in an exponential increase in computational power for specific problem types, particularly those used in cryptography.
To put this into perspective:
- A classical computer tests solution sequentially
- A quantum computer can evaluate vast solution spaces simultaneously
This unique capability is precisely what makes the discussion of quantum-resistant encryption urgent. It’s not about faster hacking; it’s about bypassing the assumption that makes classic encryption secure. Additionally, as quantum hardware continues to improve its error correction and stability capabilities, the gap between theoretical capability and practical application continues to shrink, bringing organizations closer to real-world quantum attacks.
Shor’s Algorithm: The Algorithm That Breaks Everything
This algorithm is widely seen as the single biggest threat to classic encryption systems. Developed in 1994, Shor’s Algorithm provides an effective way of factoring large integers, something that traditional computers struggle with. This directly weakens the security of RSA and other public-key systems.
The following are top 3 reasons why it’s so powerful:
- It transforms a problem considered “computationally infeasible” into a solvable one.
- It scales efficiently with larger numbers, unlike classical methods.
- It enables direct recovery of private keys from public keys.
In practical terms, this means that organizations’ encrypted communications, digital signatures, and financial transactions could all be compromised in the blink of an eye. What makes this situation even worse is the “speed.” Under ideal conditions, quantum systems running Shor’s Algorithm could bypass encryption in hours instead of millennia. This is the point where conventional cryptography fails and where post-quantum encryption becomes essential for survival.
Grover’s Algorithm: Weakening Even Strong Systems
While Shor’s Algorithm targets asymmetric encryption, Grover’s Algorithm focuses on symmetric encryption systems like Advanced Encryption Standard (AES). Instead of breaking encryption, this method accelerates brute-force attacks.
Here’s how:
- It reduces the number of operations needed to guess a key.
- It effectively halves the security strength of symmetric algorithms.
For example:
- AES-128 becomes vulnerable at a much lower computational cost.
- AES-256, while still strong, loses a significant portion of its security margin.
This means that even quantum-safe systems in the past need reassessment. Grover’s Algorithm reinforces the need for quantum-proof encryption, where security models account for quantum-backed attacks, not just traditional ones. The point to be noted here is that the quantum threat is not limited to one type of encryption; it revolves around the entire cryptographic ecosystem
The Timeline is Shorter Than Expected
For decades, quantum threats were assumed theoretical with no practical impact. However, that narrative is rapidly changing with recent computing advancements, and it is suggested that breaking encryption may not require millions of qubits as believed previously. Instead, it’s assumed that nearly 10,000 high-quality qubits could be sufficient to break widely used cryptographic systems. This significantly accelerates the expected timeline.
Current projections indicate:
- 10–15 years for large-scale, fault-tolerant quantum computers
- Earlier breakthroughs possible due to rapid investment and innovation
- Governments and private sector organizations actively racing toward quantum advantage
The Invisible Risk: Data is Already Being Targeted
The darkest side of the quantum threat is that it does not require immediate capability to cause damage. The Harvest Now, Decrypt Later (HNDL) strategy is already in motion. Cyber attackers are intercepting encrypted data today, storing it in massive volumes, and waiting for quantum computers to unlock it in the future. This is creating a time-delayed vulnerability, as sensitive data, including financial records, healthcare information and government communications, which often retains value for years, can be transmitted securely today could be exposed in the future without any additional breach.
This is why quantum encryption strategies must address both present and future threats. Organizations that fail to account for HNDL risks are effectively leaving a backlog of exploitable data for future attackers.
Why This Changes Everything for Businesses
The effects of quantum decryption extend far beyond technical systems; they have implications for the entire business landscape.
When encryption fails, it can lead to:
- Immediate exposure of sensitive customer data
- Loss of intellectual property and competitive advantage
- Regulatory penalties and legal consequences
- Long-term reputational damage
In industries like defence, healthcare, government, and finance, the stakes are even higher, as a single quantum-backed attack could compromise decades of encrypted data in one breach. This is why organizations are shifting toward quantum-resistant cryptography as part of broader risk management and cybersecurity strategies.
The Evolution: From Classical to Quantum Safe Encryption
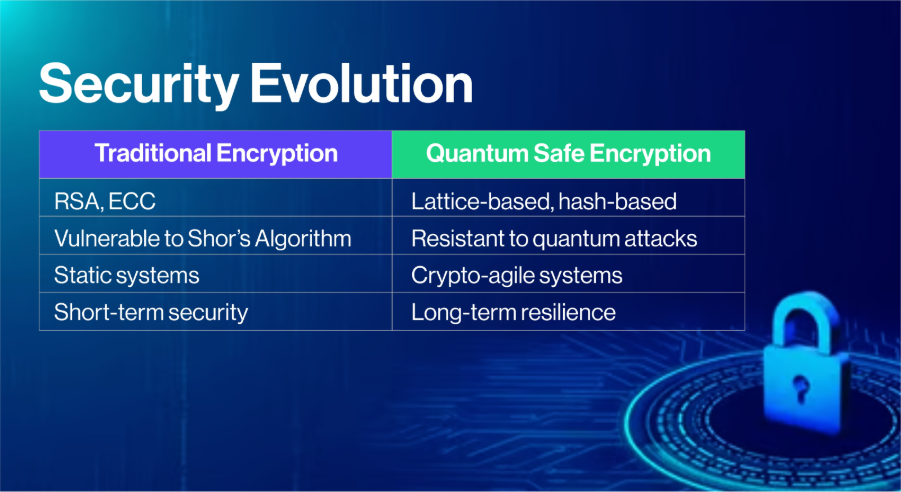
Despite the emerging risks, encryption itself is not becoming obsolete; it’s evolving. Thus, researchers are actively developing post-quantum cryptography methods designed to withstand quantum attacks, including:
- Lattice-based cryptography (resistant to both classical and quantum attacks)
- Hash-based cryptography (used for secure digital signatures)
- Code-based cryptography (with decades of proven resilience)
These approaches form the backbone of quantum safe cryptography. However, quantum-transitioning to these systems presents challenges:
- Compatibility with existing infrastructure
- Performance considerations at scale
- Long migration timelines across distributed systems
This is why organizations must approach post-quantum encryption as a phased transformation, not a one-time upgrade.
Why Quantum Encryption Requires a Strategic Approach
The transition to quantum-resistant systems is not just technical, it’s strategic. This means, quantum risk has unique characteristics which require tailored strategic response.
Some of the unique characteristics, includes:
- It introduces delayed but irreversible exposure
- It affects data already in storage, not just future communications
- It requires long-term planning and execution
This is why quantum-proof encryption strategies are becoming essential. A comprehensive approach includes:
- Crypto-agility: Ability to switch algorithms without rebuilding systems.
- Hybrid Encryption Models: Combining classical and post-quantum methods.
- Risk-based Prioritization: Protecting high-value data first.
- Continuous Monitoring: Adapting as quantum capabilities evolve.
Thus, organizations that treat this as a gradual transition will be better positioned than those forced into reactive changes later.
How QEncrypt Defines the Future of Quantum-Resistant Security
As the shift toward quantum encryption accelerates, organizations need more than awareness; they need execution and leadership. QEncrypt is built to address this exact challenge. Rather than offering point solutions, QEncrypt provides a forward-looking framework that enables organizations to:
- Implement quantum resistant encryption across critical systems
- Transition seamlessly to post quantum cryptography
- Protect against Harvest Now, Decrypt Later risks
- Maintain long-term data security and compliance
By combining advanced cryptographic design with real-world deployment strategies, this tool helps organizations move from reactive defence to proactive resilience.
In a world where encryption is being redefined, QEncrypt stands at the forefront, helping define what secure means in the quantum era.
Final Thoughts
This is a sure thing that quantum computing will not eliminate encryption, but it will fundamentally redefine it. The systems that protect today’s digital infrastructure were designed for a world constrained by classical computing limits, and those limits are rapidly disappearing. As quantum capabilities advance, the risk will not emerge gradually, it will arrive suddenly, exposing years of previously secure data.
Therefore, organizations that fail to act early may discover that their most valuable information has already been compromised. The transition toward quantum encryption, quantum safe encryption, and post quantum cryptography is no longer optional, it is inevitable. The organizations that succeed in this new era will be those that prepare in advance, adopt flexible security strategies, and prioritize long-term resilience over short-term convenience.